SysAdmin Horror Stories – FREE eBook

Last year’s ebook, SysAdmin Horror Stories Vol1 by Altaro, highlighted some of SysAdmins’ funniest and most horrifying stories. It proved so successful, that Altaro decided to produce a second edition this year: they’ve gathered some more real-life stories to share with you, that are both funny and horrific!
We all know that a SysAdmin’s job is no easy task, and apart from constantly having systems to update, bugs to fix and users to please, SysAdmins encounter all sorts of situations throughout their careers. From tech situations to funny anecdotes, terrible mishaps or incidents with colleagues, this eBook includes real stories of what SysAdmins go through on a daily basis.
It’s very easy to download as no registration is required. Click on Download and it’s yours. It includes more than 20 short stories but this one is my personal favourite 😊.
Backup Product Review
5 years ago, I was asked to review a beta of a backup product called Altaro. 5 years on, I’m reviewing the product to see how far it has come along. The first step is to download a copy of the software from Altaro.com, which was painless, and I went for the 30-day full trial. It has to be said they have a free community edition too, which is great for those who want to protect their home labs.
As before, I’m scoring my experience 0 to 5 . 0 being bad and 5 being really good.

I will review/evaluate Altaro using my home lab based on VMware vSphere 7.
Ease of prerequisites:
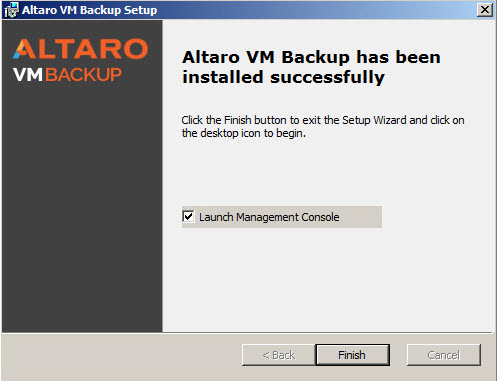
- As you can see, its just a single executable and straightforward install.
- I only had to deploy a windows server that met the perquisites >HERE<
- Altaro installed any prerequisites for me
- Score = 4 – I kept the score the same as I’m a believer in the virtual appliance way of doing things and never happy having to deploy a windows licensed VM
Ease of Install:
- Super simple to install
- Next next next, that’s all it took. Really it is that simple to deploy
- Score = 5

Time to Deploy:
- Very very quick install. It took no time at all. If you compare install time to other products on the market, you’ll know setup time can be mundane.
- Score = 5
Ease of post-install config:
- Prompts you to walk through steps
- Very simple to attach the source i.e. Vmware or Hyper-V
- Target locations can be a physical disk or network share
- And my favorite option is a secondary offsite target, which can be an S3 type bucket on one of the public clouds.
- Score = 4 < I upgraded the score from 2015 down to its pure simplicity

Ease of setting up a job:
- This part always catches me off guard. I’m not sure if I’m doing it wrong, but I cannot figure out how to select I want a whole datacenter to be backed up and right now the expectation is to choose each VM one by one into a standard backup
- However again Altaro is flipped on its head. The idea is to set up the schedule first then add-in source machines later. To do that, you simply drag and drop the infrastructure to the schedule.
- Score = 4 < upgraded due UX experience. Software shouldn’t be complicated to use, and Altaro is very straight forward.
Restore Job Realization:
- Completed no hassle
- Nice extra feature I didn’t see last time was boot from VM. Not the only product that can do this but nice to see here
- Score = 4
Restore Performance:
- Time to complete restore is 3 minutes to restore a VM. No issues there:
- Score = 4

File-level Restore:
- Fairly Straight forward but no option for direct restoration.
- Unsure about which file-systems it supports. < update still doesn’t seem to have Linux file-system support and offers a workaround with the boot from backup option. Altaro??? This is a must feature!
- Score = 3

Self-service Portal:
- Last time I scored this as a 0, but you’ll see later that having a documented API now is the key to self-service functionality, and to offer that in an external CMP solution like vRA or CloudBolt.
- Score = 3 < upgraded
Ability to Backup VSS Apps:
- Has VSS function
- Option to truncate logs too
- Score = 5
Support for physical server:
- Last year Altaro released a free community tool to allow you to Backup a physical server and restore it as VMs. Great as now there is a solution for physicals, but the contention I have with this is that the reason you might have physical servers is that you cannot run the application on a VM. So ending up with a restore on a VM might not be advantageous. I upgraded the score as it’s a big improvement on 2015, but needs more work. To find out more about this tool Click >HERE<
- Score = 3
DR capabilities:
- Offsite capabilities. This is a must for some organizations. This negates the need to store an offsite tape, for example.
- Since 2015 a replication feature has been added, which allows you to replicate to an Altaro Offsite Server. The Offsite Server acts as a target for copying backups over to a remote location. In a disaster, you can boot up at the remote site.
- Score = 5 < big upgrade in the score since 2015
Data Availability:
- Nice sandbox feature
- Score = 4
API functionality:
- Update since 2015 – now documented REST API
- This is a must IMO since I work in a managed services setting and the lead in automation in my company. No API, No Automation. Click >HERE< to review the API documentation
- Score = 4
Multi-hypervisor:
- Hyper-V
- VMware
- Score = 3. Seems low but comparable to other products on the market.
Multi-Cloud:
- Only as an offsite target
- No cloud support for source infrastructure. This is a gap for me. Altaro is a great (one of the best) products for on-prem virtual infrastructure but is behind on cloud support. You could argue that most companies are still on-prem, but given what just happened in COVID19 we see a surge of migration to cloud looming. No company wants to be responsible for an on-prem datacenter anymore.
- Score = 2
Unreviewed feature:
- O365 Backup – you can back up and restore all your Office 365 mailboxes and files stored in OneDrive and SharePoint through, and you can centrally manage and monitor your backups through Altaro’s cloud-based management console. You also get unlimited backup storage. Click >HERE< to find out more
- Score = 4 < even though I didn’t review this feature, it’s a notable feature.
Bonus Feature:
- In-app support chat – gotta love that, right? In the Altaro console, you fire up a chat window and talk to Altaro support staff. I didn’t have to wait more than a few seconds. I had no problems to report but just wanted to test what would happen. Awesome feature!
- Score = 5

Conclusion – Altaro, while I’d like to see more cloud support, is a great solution. Reasonably priced and hits the mark for many organizations. It was super simple to use, and from an on-prem perspective doesn’t lack many features. If you know me and know me well, you know the whole API thing was at the top of my list of wants, and Altaro doesn’t disappoint there too. Overall a great product!
Installing ESXi 7 on a Intel NUC 10
With all my other hobbies like 3D printing, micro-controllers, and DJ-ing I’m quickly running out of space at home. My kids insist that the house not be used as a man cave, so I’ve ended up with numerous sheds in the garden. I have a beefy lab with four servers totaling 320GB of RAM and couldn’t justify buying into the whole Intel NUC way of life. Now I want to downsize, so I have invested in my first NUC. I cannot afford at £750 a pop to replace all my servers in one go, but the idea is one at a time. I purchased a bare-bones NUC10 core i7 with 64GB of RAM. I knew I needed at least 2 NICs, so following William Lam’s blog, I purchased a StarTech USB NIC.
The first step was to install the memory, which was very straight forward. Undo the 4 screws on the bottom of the NUC, and that exposed the motherboard. Just a case of inserting the 2 x 32GB DDR4 memory sticks. I did notice that this NUC can take both SATA and NVMe disks. I needed neither since, in my lab, I always boot ESXi from USB disk.

The next thing I had to do was prepare a custom iso as I’d read on William Lam’s blog to make the StarTech USB NIC work I would have to install the Native USB NIC drivers, which were a FLING. So I downloaded ESXi-Customiser so I could easily make a new ESXi 7 iso that had the USB driver embedded into it. ESX-Customiser is no longer developed but still work if you hacked the .cmd file to stop it checking for a windows version by adding a REM statement at the beginning:

The idea is you point it as an existing iso file of ESXi and then the driver you want to include in .vib or .zip format press go, and it makes a new iso file for you.

The next step is to use RUFUS to create a bootable USB disk with the ESXi 7 iso on it so you can install it from the USB key. Select the USB key you want to use and select the newly created iso file. Make sure you have “MBR” and “Boot or UEFI” selected. Click start, and Rufus will create the bootable ESXi7 USB key for you.

Now for me, I had another USB disk, which I plan to install ESXi on. I inserted both USB keys into the NUC and powered it on. ESXi 7 started to install, but seconds later, I got a PSOD with an error saying failed to verify signatures of the following vibs… it was not happy with the USB native driver.

The workaround was to disable Secure Boot in the BIOS, and the install continued on. The next issue I got was the installation couldn’t find the onboard NIC. I have been in this situation tons of times with home lab installs. The issue (from memory) is VMware includes server-grade NIC drivers and not desktop drivers by default. So the Intel NE1000 driver baked into the ESXi iso was for the server version. I had to downgrade the driver with the one found >HERE< . Now the install worked and both NICs could be seen by the newly installed ESXi 7.














